Remote Sensing | Free Full-Text | On the Exploitation of Remote Sensing Technologies for the Monitoring of Coastal and River Delta Regions

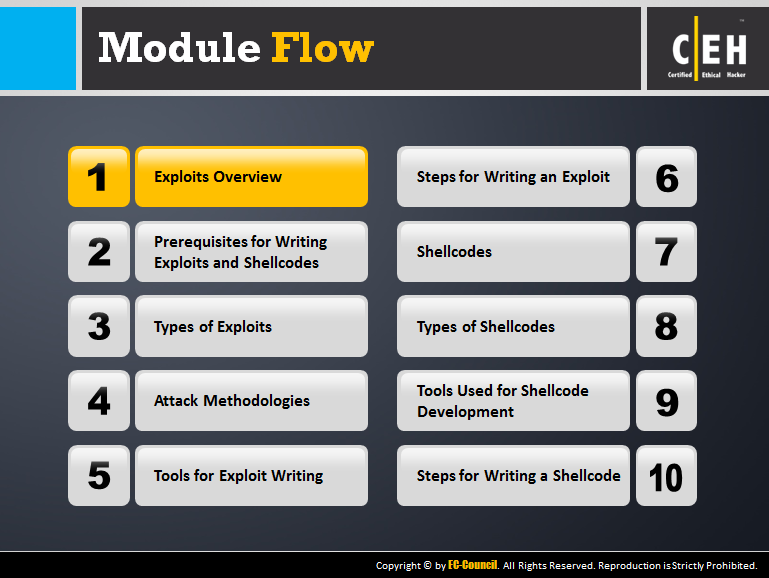
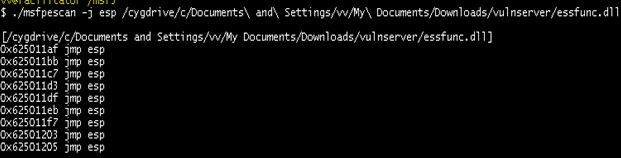
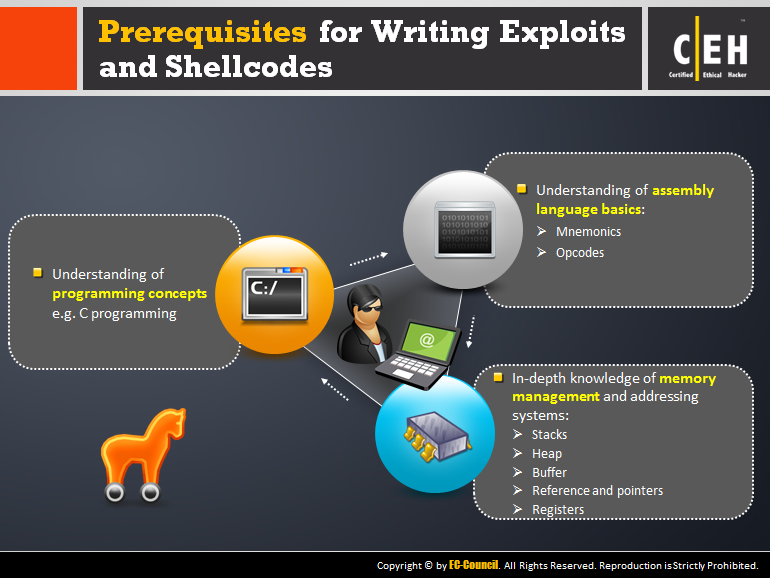
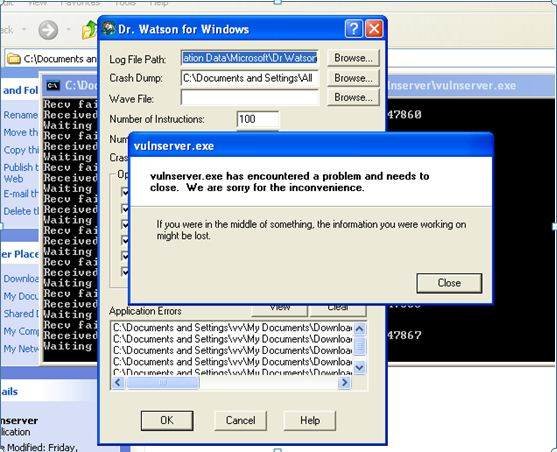
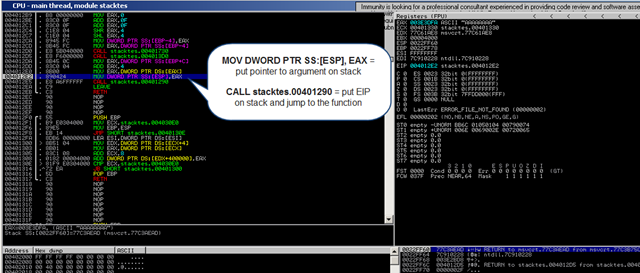
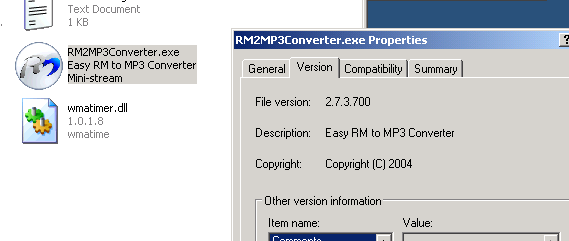
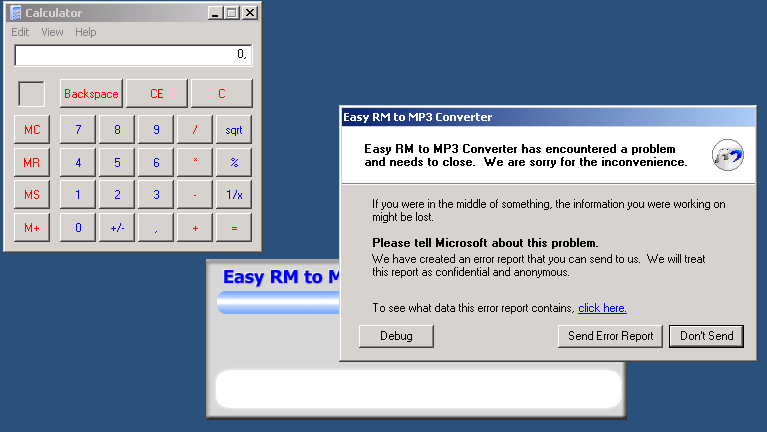
Exploit Writing | CTG Infosec - Ethical Hacking | Web Security Expert | Network Security Expert |Bug Bounty |Source Code Review |Reverse Engineering | Exploit Development | Malware Analysis |Mobile Application Security